Convertido en un valor literario seguro y con una trayectoria sólida, Máximo Huerta acaba de publicar ‘París despertaba tarde’, aventura literaria en la que recupera a Alice, personaje de ‘Una tienda en París’, y se mete de lleno en la capital francesa durante el efervescente 1924. Aquel año de Olimpiadas, de la culminación de la basílica del Sagrado Corazón, de cabarets, movimientos artísticos y bon vivants sirve al periodista y escritor para reafirmar su pasión por la cultura gala y poner en valor algo tan denostado en nuestros tiempos como la nostalgia. Cómo una persona y una ciudad pueden resurgir desde el trauma del desamor o de la guerra, respectivamente.
La vida del que fuese ministro de Cultura ha cambiado sustancialmente desde que dejó Madrid y regenta una librería, La Librería de Doña Leo, en Buñol. De ese local, de los recuerdos que lo siguen uniendo a Madrid, de su madre y de la televisión que se está haciendo en estos momentos nos habla en una entrevista en la que caben desde su visión del amor actual a sus primeros recuerdos vitales, su visión de los tiempos líquidos o la felicidad que dan las pasiones.

El autor en la ciudad que tanto ama. (Javier Ocaña)
El autor en la ciudad que tanto ama. (Javier Ocaña)
La primera pregunta es obvia, ¿por qué París y por qué Alice?
París en los años 20 me parece deslumbrante, ingeniosa, insolente. Me parece fascinante lo que sucedió en solo una década. Alice es un personaje que viene de mi ficción y que viene a retratar a las modelos que posaban entonces para los pintores. Yo lo que decido es ponerles nombre a esas modelos y crear una nueva historia.
¿La nostalgia es buena o mala?
Es sabrosona. Todo lo que tiene que ver con mirar a fetiches, a obras y a momentos históricos te deja buen sabor de boca. A mí no me entristece nada. De todas formas, lo de esta novela no es nostalgia, es la revindicación de una época.
¿Es cómodo el pasado, es un lugar seguro como decía Stefan Zweig?
Escribir de un momento tan importante es un lugar seguro, pero también lo único que tenemos. El futuro no existe. Solo existe el pasado, paradójicamente, aunque no podamos tocarlo. Pero es lo único que existe. No soy Isaac Asimov, así que prefiero hablar de cosas que sé que existen, aunque hayan pasado hace tiempo.
El libro comienza con una llamada de una persona a otra que además siempre seguirá siendo muy común: “Fulanito me ha dejado”.
Esta novela es una gran historia de amor. Una novela histórica de época. Tanto la ciudad como la protagonista están en plena metamorfosis. Por eso arranca la historia en ese momento del desamor, del dolor, de la guerra. Y sí, todo nace del desamor.
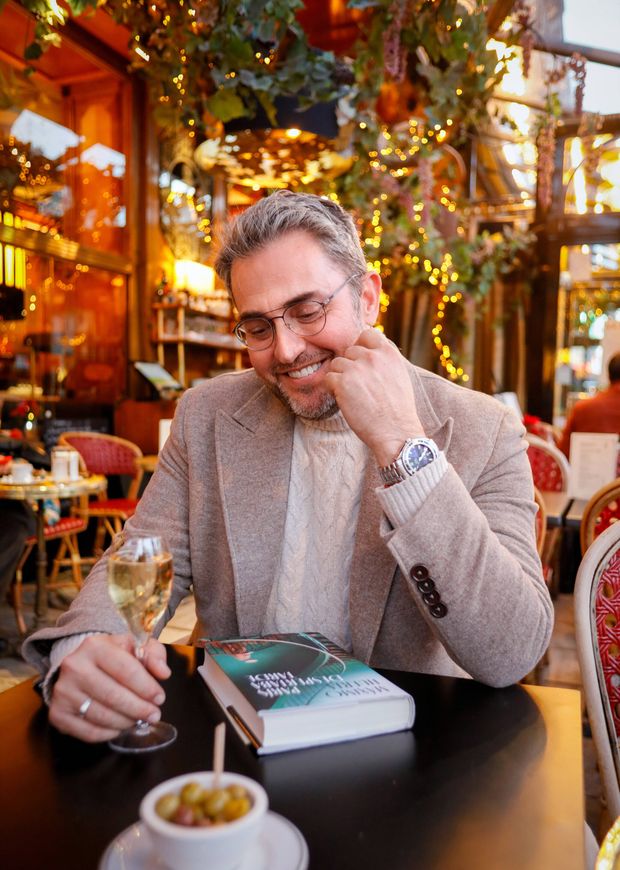
Huerta con un ejemplar de su libro. (Javier Ocaña)
Huerta con un ejemplar de su libro. (Javier Ocaña)
¿Crees, por tanto, que el desamor es una fuente de inspiración mayor que el amor?
Puede que las canciones de amor sean, a veces, muy cursis. En cambio, las de desamor suelen ser, en algunas ocasiones, boleros o bastante más potentes. El desamor es mucho más literario, mucho más musical, mucho más teatral. En el momento de felicidad, nadie se acuerda de componer, de pintar o de escribir.
Si tuviésemos que trasladar a tu protagonista al siglo XXI, ¿se ha abaratado el amor? Al convertirse en algo tan efímero y tan del ahora…
El amor ahora tiene demasiada prisa, demasiada velocidad. Es un amor de consumo porque ahora tratamos todo como consumidores. Y en otros momentos se ha hecho más como los chinos o los japoneses, con su arte de arreglar las piezas para que sigan sobreviviendo. Estoy muy a favor de esa reconstrucción para hacerlo todo más duradero.
Si el amor es consumo y hoy nace en las redes y aplicaciones, ¿podría decirse que todos nos vendemos un poco?
Totalmente. Todos nos ofrecemos más o menos, y me incluyo, como productos para los demás.
La narrativa de la historia
¿Cómo es el proceso de fabricar una historia que se entremezcla con hechos históricos?
Llevo diez años construyéndola. Me quería ajustar solo a un año, a 1924, con los Juegos Olímpicos, con el momento en el que se finaliza el Sagrado Corazón… Ajustarme a un año tan preciso me obliga a revisar qué pintores están muertos, otros no han acabado, han acabado ya… Ha sido una labor de documentación tremenda, pero muy gratificante. Sobre todo porque, como me apasiona y tengo una obsesión que culmina con esta obra, pues la he disfrutado. He tenido que buscar mucho, que meterme en prensa de los años 20, en noticias de cines, de arte, de moda…

Máximo Huerta. (Javier Ocaña)
Máximo Huerta. (Javier Ocaña)
Tuviste que hacerte esquemas, supongo. O sea que llevabas a cabo dos labores paralelas: la de escribir y la de documentarte.
Listas. Nombres. Hechos. Artistas de cine que aparecen, como Concha Piquer, lugares que estaban de moda…Tenía una pizarra con todo eso en mi habitación. Una pizarra y folios en la mesa. También he visto mucha fotografía de la época. Afortunadamente, hay muchas y además fotografiaban bastante los momentos de las fiestas. Era un poco Instagram, pero sin postureo: mostraban los bailes, las orgías, su vida diaria…
Se podría decir que París es la ciudad en la que renació mucha gente…
Sobre todo después de un dolor, el de la Gran Guerra. Como el primer objetivo es olvidar y el olvido es fundamental para la metamorfosis, unos locos vanguardistas y maravillosos deciden salir a pasarlo bien por si se acaba el mundo. Me gusta mucho el cómo afrontan el dolor en este tiempo y cómo París se convierte en lo que hoy es. Entonces fue una isla de libertad en medio de la Italia de Mussolini, de Alemania, de la Unión Soviética y los soviets, de Estados Unidos y la ley seca. De pronto, era la ciudad más cosmopolita del mundo. Es algo que no ha vuelto a pasar y que en parte fue producto de los inmigrantes. Y eso también me gusta mucho. Polacos, italianos… Eran inmigrantes que se sentían parisinos.
La ‘guerra’ del desamor
La protagonista tiene que recuperarse de su propia ‘guerra’. ¿Se podría decir que la novela es entonces una metáfora?
Eso es. Se titula ‘París despertaba tarde’ porque es como la protagonista. Está en metamorfosis, en un cambio, en la recuperación del dolor. Hay que olvidar ese dolor para empezar de nuevo. Y eso le ocurre tanto a la ciudad como a la protagonista.
¿Cuál es el germen de tu pasión por lo francés?
Son varias cosas. Viene de unas tías emigrantes, francesas, que vienen a Utiel en verano, antes de la vendimia, en septiembre, y llegan a las fiestas del pueblo. A mí me parecían exóticas: olían de otra manera, hablaban con un acento diferente… Para un niño de pueblo, eso es fascinación. Creo que de ahí nace la pasión. Luego esa pasión la alimenta aquel niño mitómano que empieza a buscar de dónde vienen esas señoras y todo lo que tiene que ver con su mundo.
Hablando de ciudades y de Madrid, ¿compartes el desencanto que tiene mucha gente ahora con la ciudad?
Ahora no es mi hogar porque no tengo mi casa aquí, pero me pone nostálgico recordar los buenos momentos. Voy pasando por sitios y me voy acordando de con quién he estado, qué he hecho aquí o allí…

Máximo Huerta. (Javier Ocaña)
Máximo Huerta. (Javier Ocaña)
¿Sientes nostalgia de Madrid?
Para mí tiene una mirada incluso irónica. O sea, la voy mirando ahora pensando lo lejos que ha quedado ese tiempo en el que era mi casa. Me parece que hace mucho tiempo y en realidad hace muy poquito, pero parece que haya pasado un siglo. Eso es lo que creo que provocó la pandemia. Yo me fui en 2020, cuando dejé Televisión Española.
Televisión de líderes
Y la televisión, ¿la echas de menos? ¿Qué te parece la que se está haciendo ahora?
Ahora todos son líderes. De hecho, hay dos palabras que se han explotado mucho: líder y exclusiva. Se han gastado hasta el paroxismo. Si aparece algún programa que a mí me gusta y piensan en mí, que a lo mejor ya no se acuerdan, lo hago. A mí es un medio que me sigue gustando, me sigue pareciendo un entretenimiento maravilloso. Es un electrodoméstico adictivo y algo que veo en mi madre: la tele le hace compañía. A ella le gusta oír voces y entonces yo desconecto y puedo estar, en ese rato, escribiendo o leyendo mientras mi madre está mirándola.
Pero ahora supongo que hay fronteras que no traspasarías si aceptases un programa…
Han cambiado mis prioridades, tengo otra edad y otros gustos también. Hay cosas que no volvería a hacer.
¿Y las plataformas qué te parecen?
Las plataformas son frías. Cuando mi madre se ha dormido, el salón es para mí y me pongo una película que decido cuándo empieza y cuándo acaba. Todas las teles están ahí. Lo que me parece curioso es que están compitiendo entre ellas mismas cuando la verdadera competencia son las plataformas. Creo que se han equivocado.
¿Qué tal va tu librería?
Bien, intento que mantenga un espíritu diferente. Las que se convierten simplemente en comercios me resultan frías. Si existe un turismo de librerías es porque venden historias más allá de lo que puedan tener en catálogo. En la nuestra abrimos champán por las tardes, por ejemplo. Para mí es un pequeño refugio y un juego adulto.
Si tuvieras una máquina del tiempo y te encontrases contigo mismo a los 15 años, ¿qué consejo te darías?
Baila y juega más. Vete de Erasmus. Aprende otro idioma, viaja y baila. Además, no creo en el arrepentimiento, es absurdo y una pérdida de tiempo. De lo único que nos arrepentimos es de exprimir más algo, porque nos creemos que somos inmortales, que tendremos otra oportunidad para bailar o para hacer más cosas.
News Related-
Guía práctica para animarte a combinar estampados y conseguir los mejores looks
-
La mujer de Ion Aramendi pasa por una delicada operación: "Ha sido una decisión complicada"
-
Baja el dólar, pero no paran de subir los precios
-
Confirmado: Belgrano será el rival de River en cuartos de final de la Copa de la Liga
-
Boca afuera de la Libertadores y River festeja: se clasificó al Super Mundial de Clubes 2025
-
La Selección Argentina se mide ante Alemania por un lugar en la final del Mundial Sub 17: hora, TV y posibles formaciones
-
Jennie de BLACKPINK lució un vestido pegado al cuerpo, con sus hombros al aire, y la red se prendió fuego
-
River clasificó al Mundial de Clubes 2025
-
“Llaryora se va con un impuestazo como con el que llegó hace cuatro años”
-
Milei, en Estados Unidos: almorzó con Bill Clinton y tendrá contactos con el Gobierno de Biden y el FMI
-
Javier Milei almorzó con Bill Clinton y Chris Dodd: les expuso su programa de gobierno
-
Luis ventura le ofreció trabajo a Morena y le dejó un contundente mensaje a Jorge Rial
-
Robots humanoides y puestos de trabajo: expertos adelantan los cambios que ocurrirán para 2035
-
San Lorenzo ganó su partido, clasificó a la Copa Libertadores 2024 y lo dejó sin chances a Boca
